Android malware drops Banker from PNG file
Meanwhile I found same or very similar version of this Trojan dropper and banker without obfuscation and protection by DexProtector. Dropping method and functionality is preserved. For those interested, I added hashes of infected files at the bottom.
Nowadays is malware trying to hide wherever it is possible to get under the radar of anti-virus companies. Lately I found Trojan dropper carrying malicious payload, encoded by base64, embedded inside an image file. It’s nothing special these days but it is very rare dropping technique. In the most cases are malware authors lazy enough to not even encrypt the payload file.
In the time of writing this blog post is this Trojan dropper still available to download from attacker server (hxxp://jackdojacksgot.ru/img/Update.apk). Based on VirusTotal is detection for this Trojan dropper very poor.
Nowadays is malware trying to hide wherever it is possible to get under the radar of anti-virus companies. Lately I found Trojan dropper carrying malicious payload, encoded by base64, embedded inside an image file. It’s nothing special these days but it is very rare dropping technique. In the most cases are malware authors lazy enough to not even encrypt the payload file.
Analysis
In the time of writing this blog post is this Trojan dropper still available to download from attacker server (hxxp://jackdojacksgot.ru/img/Update.apk). Based on VirusTotal is detection for this Trojan dropper very poor.
Figure 1 VirusTotal detection |
This malicious application masquerade itself as Adobe Flash Player. Based on alternative names I found in application resources malware name can be different in the other versions like: Viber New, App4porno,CommBank, My Online Security, Viber or Whatsapp.
Figure 2 Possible Trojan dropper names |
After launch, Trojan will immediately drop and request user to install Adobe Flash Player. But first let’s take a look on dropping technique.
In app assets there is nothing else to drop other than image file.
Figure 3 Trojan dropper assets |
There is only one image of dices stored in assets, but it size is more than 3.6 MB and that’s bit suspicious.
After inspecting the code application wasn’t dropping this PNG file. The Trojan dropper at first opens this image file and searches for delimiter string, in this case "12345678901234567890". Right after this delimiter is stored another application encoded by Base64.
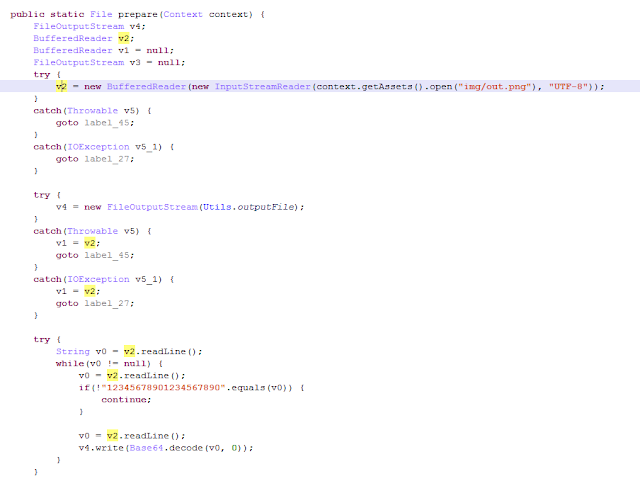 |
Figure 4 Dropping embedded malware |
Figure 5 Binary view of PNG file |
Decoded data are then stored on external storage as “prefix.apk” and demand to install. Decoded application, prefix.apk, is heavily obfuscated Android banker, stealing user credentials.
After installation it requests user to activate Administrator rights for application. This is the simplest method that prevents to uninstall this Trojan.
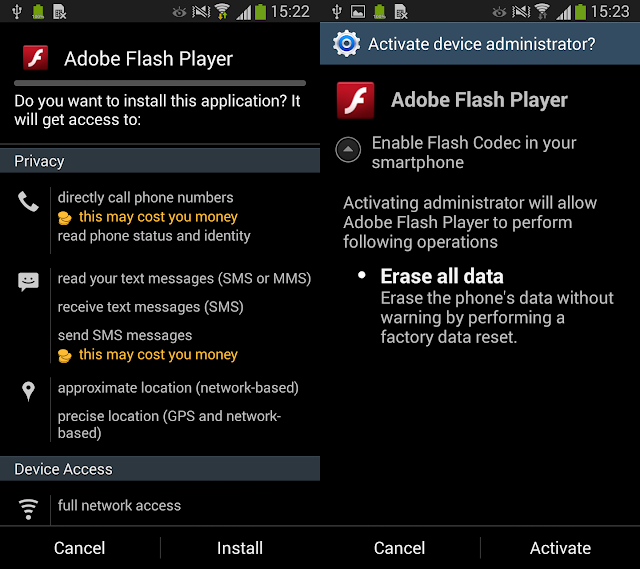 |
Figure 6 Banker install and device administrator request |
If user tries to deactivate Administrator rights then is repeatedly asked to activate it again. There are two ways how to get rid of this nasty banker. Either by going to safe mode of your device and deactivate Administrator rights and uninstall it or by using Android Debug Bridge (adb) and uninstall it from your computer.
Both apps Trojan dropper and dropped banker are the most probably obfuscated and protected by DexProtector. It’s very complicated to analyze it statically without any dynamical intervention.
Figure 7 Code obfuscation |
Banker can steal user login credentials or credit card information with phishing technique. When user opens his mobile banking application or just Google Play Store, malicious activity will be displayed on the top of the official application. This way user can be easily fooled and insert sensitive information to banker pop-up window.
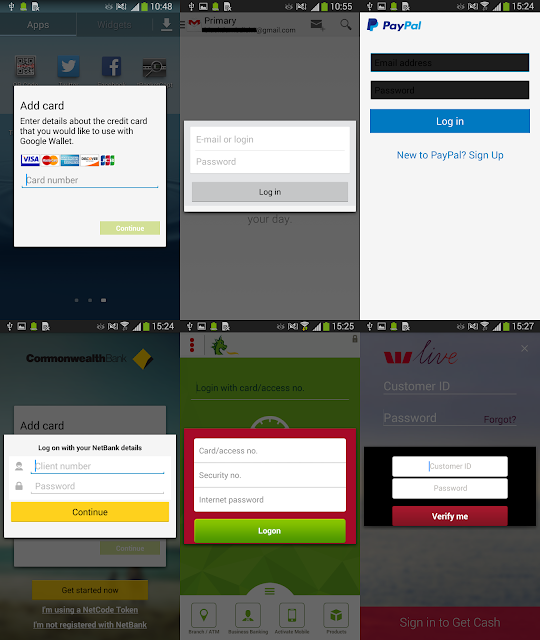 |
Figure 8 Bankers phishing windows |
User credentials are immediately sent to remote server.
Figure 9 Send stolen credentials for Gmail app |
Figure 10 Send stolen credentials for CommBank app |
Figure 11 Send stolen credentials for PayPal app |
This banker is very popular. Lately I tweeted about same banker but stored on different server.
More information
HASH dropper: 1F41BA0781D51751971EE705DFA307D2
HASH PNG: 575551FBC343EC8E1A1C771D81963096
HASH dropped: 90886B56372F5191A78A20DCB3F9FE6E
Download link: http://jackdojacksgot.ru/img/Update.apk
Remote server: 75jng75ufnf.ru:2080
Not obfuscated samples by DexProtect:
HASH dropper: E3CCAA1EF68CC472AB8983419BE15A49
HASH dropper: D4FAA81ABA663A825BB13F17E3CE3D07
HASH PNG: 6F394038D39F76F4475E1B98AD186A40
HASH PNG: BEDC1B7A2ED127C5A7E5261F043CAFE4
HASH dropped: 41C9ADD2BE9F4B04047AB232EB08058F
HASH dropped: 1B1ACD068461A074BE1A49DF02B10B09
Source:b0n1.blogspot.com
